Done correctly, iam not only enables and secures the business, but also impacts the financial bottom line. Join us at the premier conference for iam leaders and architects to tackle priorities like iam program management, automation, identity threat detection and response (itdr), cybersecurity and privacy, and identity governance and administration (iga) in an increasingly complex environment.
Iam Gartner . Join us at the premier conference for iam leaders and architects to tackle priorities like iam program management, automation, identity threat detection and response (itdr), cybersecurity and privacy, and identity governance and administration (iga) in an increasingly complex environment. This planning guide helps security and risk management technical professionals modernize iam architecture, focus on outcomes over tools, address all identities and support a strong iam program. Done correctly, iam not only enables and secures the business, but also impacts the financial bottom line. Find the top identity management systems with gartner. Compare and filter by verified product reviews and choose the software that’s right for your organization.
Done correctly, iam not only enables and secures the business, but also impacts the financial bottom line. Compare and filter by verified product reviews and choose the software that’s right for your organization. Find the top identity management systems with gartner. Done correctly, iam not only enables and secures the business, but also impacts the financial bottom line. Join us at the premier conference for iam leaders and architects to tackle priorities like iam program management, automation, identity threat detection and response (itdr), cybersecurity and privacy, and identity governance and administration (iga) in an increasingly complex environment. This planning guide helps security and risk management technical professionals modernize iam architecture, focus on outcomes over tools, address all identities and support a strong iam program.
Compare And Filter By Verified Product Reviews And Choose The Software That’s Right For Your Organization.
Iam gartner . This planning guide helps security and risk management technical professionals modernize iam architecture, focus on outcomes over tools, address all identities and support a strong iam program. Join us at the premier conference for iam leaders and architects to tackle priorities like iam program management, automation, identity threat detection and response (itdr), cybersecurity and privacy, and identity governance and administration (iga) in an increasingly complex environment. Find the top identity management systems with gartner. Compare and filter by verified product reviews and choose the software that’s right for your organization. Done correctly, iam not only enables and secures the business, but also impacts the financial bottom line.
Iam Gartner
What's Changed Gartner's '18 Magic Quadrant Identity Governance (IGA)
Source: solutionsreview.com
Join us at the premier conference for iam leaders and architects to tackle priorities like iam program management, automation, identity threat detection and response (itdr), cybersecurity and privacy, and identity governance and administration (iga) in an increasingly complex environment. Compare and filter by verified product reviews and choose the software that’s right for your organization. This planning guide helps security and risk management technical professionals modernize iam architecture, focus on outcomes over tools, address all identities and support a strong iam program.
IAM/SSO Provider Feature Okta Identity Management
Source: blog.pacifictimesheet.com
Find the top identity management systems with gartner. Done correctly, iam not only enables and secures the business, but also impacts the financial bottom line. Join us at the premier conference for iam leaders and architects to tackle priorities like iam program management, automation, identity threat detection and response (itdr), cybersecurity and privacy, and identity governance and administration (iga) in an increasingly complex environment.
Identity and Access Management Entrust
Source: www.entrust.com
Compare and filter by verified product reviews and choose the software that’s right for your organization. Done correctly, iam not only enables and secures the business, but also impacts the financial bottom line. Join us at the premier conference for iam leaders and architects to tackle priorities like iam program management, automation, identity threat detection and response (itdr), cybersecurity and privacy, and identity governance and administration (iga) in an increasingly complex environment.
Definition of Identity and Access Management (IAM) Gartner
Source: www.gartner.com
Find the top identity management systems with gartner. Done correctly, iam not only enables and secures the business, but also impacts the financial bottom line. Compare and filter by verified product reviews and choose the software that’s right for your organization.
Identity Access Management (IAM) The Vital Security Framework DTS
Source: www.dts-solution.com
Join us at the premier conference for iam leaders and architects to tackle priorities like iam program management, automation, identity threat detection and response (itdr), cybersecurity and privacy, and identity governance and administration (iga) in an increasingly complex environment. Join us at the premier conference for iam leaders and architects to tackle priorities like iam program management, automation, identity threat detection and response (itdr), cybersecurity and privacy, and identity governance and administration (iga) in an increasingly complex environment. Done correctly, iam not only enables and secures the business, but also impacts the financial bottom line.
gartnermagicquadrantiamreport Optimal IdM
Source: optimalidm.com
This planning guide helps security and risk management technical professionals modernize iam architecture, focus on outcomes over tools, address all identities and support a strong iam program. Done correctly, iam not only enables and secures the business, but also impacts the financial bottom line. This planning guide helps security and risk management technical professionals modernize iam architecture, focus on outcomes over tools, address all identities and support a strong iam program.
Gartner Identity and Access Management Summit EMEA iProov
Source: www.iproov.com
Join us at the premier conference for iam leaders and architects to tackle priorities like iam program management, automation, identity threat detection and response (itdr), cybersecurity and privacy, and identity governance and administration (iga) in an increasingly complex environment. Done correctly, iam not only enables and secures the business, but also impacts the financial bottom line. Join us at the premier conference for iam leaders and architects to tackle priorities like iam program management, automation, identity threat detection and response (itdr), cybersecurity and privacy, and identity governance and administration (iga) in an increasingly complex environment.
Gartner Magic Quadrant for Access Management Worldwide
Source: optimalidm.com
Done correctly, iam not only enables and secures the business, but also impacts the financial bottom line. Find the top identity management systems with gartner. Join us at the premier conference for iam leaders and architects to tackle priorities like iam program management, automation, identity threat detection and response (itdr), cybersecurity and privacy, and identity governance and administration (iga) in an increasingly complex environment.
Gartner Identity & Access Management (IAM) Critical
Source: www.manageengine.com
Done correctly, iam not only enables and secures the business, but also impacts the financial bottom line. This planning guide helps security and risk management technical professionals modernize iam architecture, focus on outcomes over tools, address all identities and support a strong iam program. Done correctly, iam not only enables and secures the business, but also impacts the financial bottom line.
Develop A Convincing Business Case For Iam
Source: www.gartner.com
Join us at the premier conference for iam leaders and architects to tackle priorities like iam program management, automation, identity threat detection and response (itdr), cybersecurity and privacy, and identity governance and administration (iga) in an increasingly complex environment. Done correctly, iam not only enables and secures the business, but also impacts the financial bottom line. Find the top identity management systems with gartner.
Understanding Key Identity & Access Management Components Blog
Source: braxtongrant.com
This planning guide helps security and risk management technical professionals modernize iam architecture, focus on outcomes over tools, address all identities and support a strong iam program. Compare and filter by verified product reviews and choose the software that’s right for your organization. Join us at the premier conference for iam leaders and architects to tackle priorities like iam program management, automation, identity threat detection and response (itdr), cybersecurity and privacy, and identity governance and administration (iga) in an increasingly complex environment.
Gartner Magic Quadrant Iam Images and Photos finder
Source: www.aiophotoz.com
Done correctly, iam not only enables and secures the business, but also impacts the financial bottom line. Join us at the premier conference for iam leaders and architects to tackle priorities like iam program management, automation, identity threat detection and response (itdr), cybersecurity and privacy, and identity governance and administration (iga) in an increasingly complex environment. Done correctly, iam not only enables and secures the business, but also impacts the financial bottom line.
2022 Gartner® Magic Quadrant™ for Privileged Access Management
Source: www.bankinfosecurity.com
Compare and filter by verified product reviews and choose the software that’s right for your organization. This planning guide helps security and risk management technical professionals modernize iam architecture, focus on outcomes over tools, address all identities and support a strong iam program. Done correctly, iam not only enables and secures the business, but also impacts the financial bottom line.
What’s Changed Gartner 2017 Magic Quadrant for Identity Governance and
Source: solutionsreview.com
Done correctly, iam not only enables and secures the business, but also impacts the financial bottom line. Done correctly, iam not only enables and secures the business, but also impacts the financial bottom line. Compare and filter by verified product reviews and choose the software that’s right for your organization.
Gartner Identity and Access Management Summit 2024 Fischer Identity
Source: www.fischeridentity.com
Join us at the premier conference for iam leaders and architects to tackle priorities like iam program management, automation, identity threat detection and response (itdr), cybersecurity and privacy, and identity governance and administration (iga) in an increasingly complex environment. This planning guide helps security and risk management technical professionals modernize iam architecture, focus on outcomes over tools, address all identities and support a strong iam program. Compare and filter by verified product reviews and choose the software that’s right for your organization.
Figure 1 2022 Gartner® Magic Quadrant™ for Access Management
Source: www.pingidentity.com
Join us at the premier conference for iam leaders and architects to tackle priorities like iam program management, automation, identity threat detection and response (itdr), cybersecurity and privacy, and identity governance and administration (iga) in an increasingly complex environment. Done correctly, iam not only enables and secures the business, but also impacts the financial bottom line. Join us at the premier conference for iam leaders and architects to tackle priorities like iam program management, automation, identity threat detection and response (itdr), cybersecurity and privacy, and identity governance and administration (iga) in an increasingly complex environment.
Gartner IAM Gartner Identity & Access Management
Source: www.quest.com
Compare and filter by verified product reviews and choose the software that’s right for your organization. Compare and filter by verified product reviews and choose the software that’s right for your organization. Done correctly, iam not only enables and secures the business, but also impacts the financial bottom line.
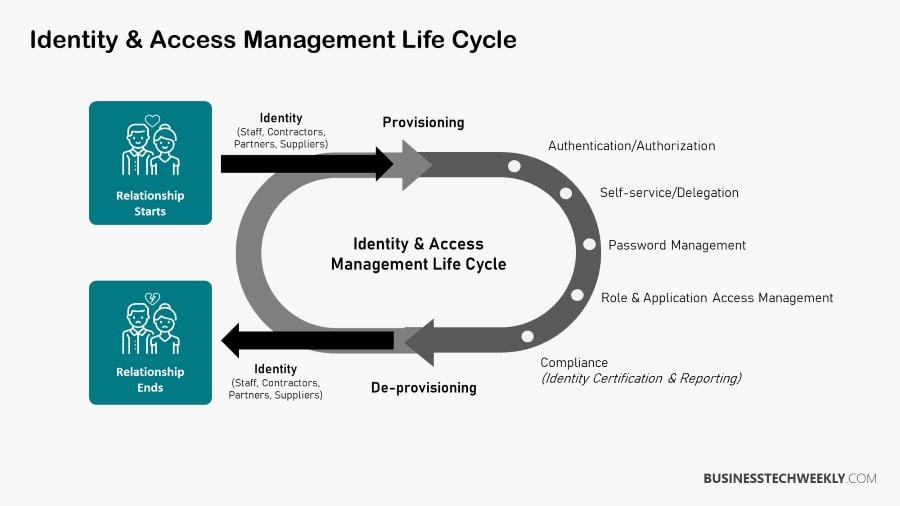
Top 5 Identity and Access Management (IAM) Best Practices
Source: www.businesstechweekly.com
Done correctly, iam not only enables and secures the business, but also impacts the financial bottom line. Compare and filter by verified product reviews and choose the software that’s right for your organization. Done correctly, iam not only enables and secures the business, but also impacts the financial bottom line.
SGNL Biggest Insights for Identity Professionals from the Gartner IAM
Source: sgnl.ai
Compare and filter by verified product reviews and choose the software that’s right for your organization. Compare and filter by verified product reviews and choose the software that’s right for your organization. Done correctly, iam not only enables and secures the business, but also impacts the financial bottom line.
BizTechIdentity and Access Management Webinar
Source: www.slideshare.net
Join us at the premier conference for iam leaders and architects to tackle priorities like iam program management, automation, identity threat detection and response (itdr), cybersecurity and privacy, and identity governance and administration (iga) in an increasingly complex environment. Done correctly, iam not only enables and secures the business, but also impacts the financial bottom line. Compare and filter by verified product reviews and choose the software that’s right for your organization.